The era of broadcasting information is due to change. Every recipient will soon receive a copy that belongs only to them.
There’s a structural assumption baked into how organizations share sensitive information that almost no one thinks about - and it’s overdue for disruption.
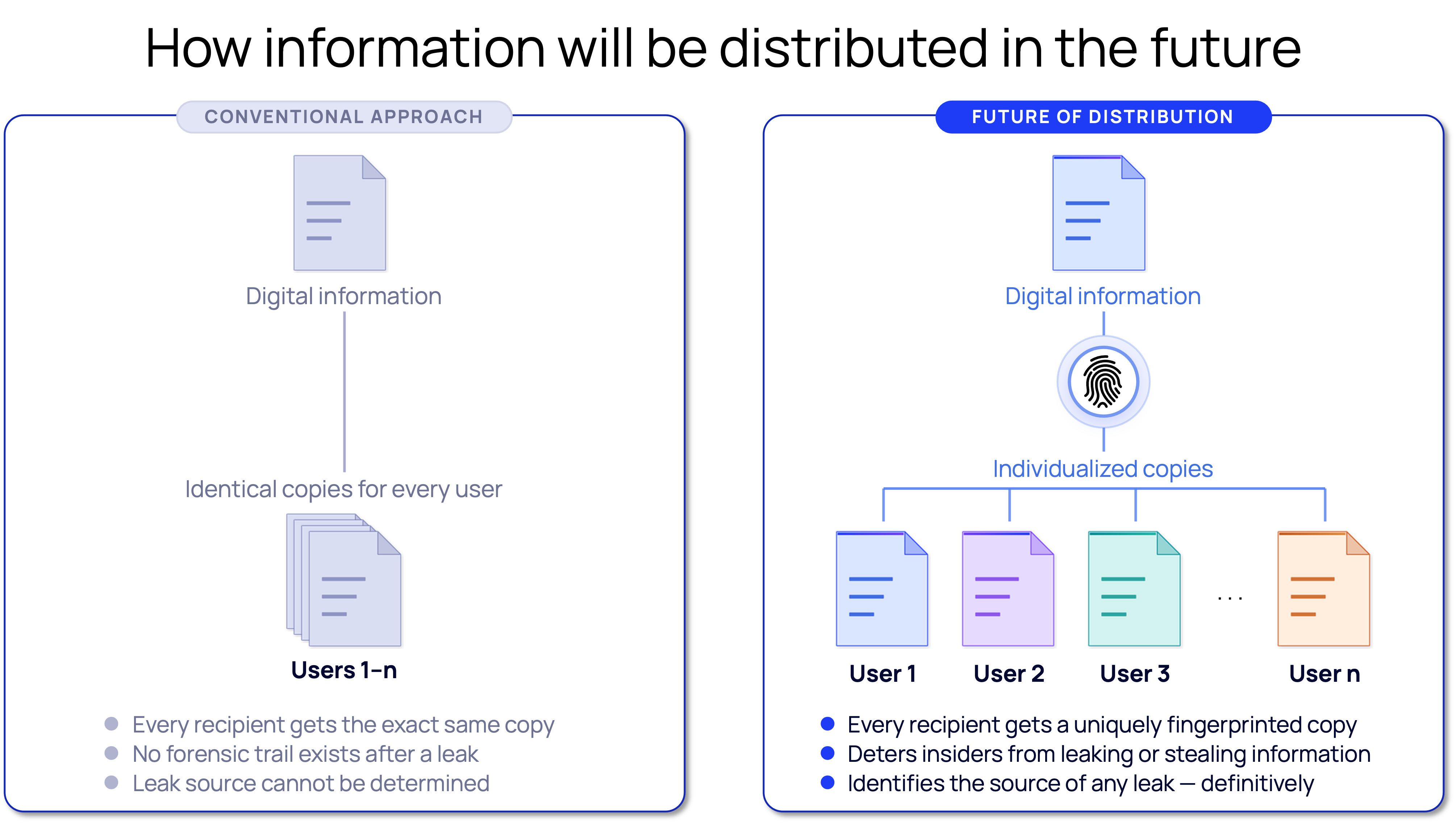
When a board deck gets distributed before an earnings call, every director receives the same file. When a law firm shares a draft agreement with the deal team, every attorney gets an identical copy. When a government agency distributes a classified brief to thirty cleared personnel, the document that lands in each inbox is indistinguishable from every other. One master version. Many copies. All the same.
This wasn’t a deliberate design choice; it was the only practical option at the time. Generating individualized versions of sensitive documents at scale - quickly, seamlessly, without disrupting workflows - simply wasn’t feasible, so organizations made a single copy and broadcast it. It was efficient, universal, and it created a security blind spot that has quietly compounded for decades.
When every recipient has the same file, forensic differentiation becomes impossible. This is a problem that only fully reveals itself after a leak, which is precisely when it’s too late.
A merger term sheet surfaces in the press the night before a deal closes. A confidential strategy deck turns up in the wrong hands. An internal analysis gets forwarded somewhere it was never meant to go. The investigation that follows is always the same: compile a list of everyone who had access, interview them, review the logs, and try to reconstruct what happened from indirect evidence. Most of the time, you don’t get to a definitive answer. Not because investigators aren’t capable, but because the architecture of the distribution itself makes forensic certainty impossible. There is no way to look at an identical copy and determine which person it came from.
What’s changing isn’t organizational intent, it’s infrastructure.
The computational constraints that made individualized distribution impractical have essentially disappeared. Modern systems make it possible to generate thousands of forensically unique copies of the same document in the time it takes to send a single email. What was prohibitively expensive five years ago is now not only possible, but being achieved by prepared organizations.
The direction of travel is clear: every recipient will receive a copy that is uniquely theirs. Differences are indistinguishable to the human eye, but forensically distinct - permanently and irrevocably marked with an identifier that ties the content to the specific person who received it. No two copies will be alike, and the content itself carries the record.
This is the same arc that played out with marketing, with media, with product experiences. Every technology category that starts with broadcast eventually becomes individualized, and sensitive information distribution is next.
Individualized distribution reshapes information security in ways that go beyond any single leak investigation.
The most immediate effect is deterrence. When people know that their copy is uniquely marked, the decision to leak or to be careless with sensitive information looks different. The question shifts from will anyone notice? to will I be identified? That change in perceived risk is itself a security control, and it operates before any investigation ever needs to begin.
When deterrence fails, attribution becomes possible in a way it never was before.The leaked document doesn’t just prove that a leak occurred, it identifies the source. The copy carries the answer. That transforms leak investigations from long, inconclusive exercises in circumstantial evidence into definitive forensic events, producing court-admissible findings rather than unresolvable suspicion.
And underlying both is a structural guarantee: there is no longer such a thing as an anonymous copy. The broadcast era assumed that once information left your hands, you lost visibility. The individualized era begins with the premise that you never do.
EchoMark was built for this transition - automatically generating uniquely watermarked copies of every protected document and email, invisibly and without any workflow disruption, integrated directly into the environments where sensitive information already moves. The technology makes individualized distribution the default, not the exception.
The future of sensitive information isn’t a single document broadcast to many. It’s a unique document, created for each person, the moment it’s sent. Schedule a demo to see how EchoMark can protect your organization's most sensitive information.